Como encontrei +100 Cross Site Scripting e SQL Injection refletidos em uma recompensa privada de bug de hackerone…
May 03 2023
.
- Subfinder:https://github.com/projectdiscovery/subfinder
- Localizador de recursos:https://github.com/tomnomnom/assetfinder
- Httpx:https://github.com/projectdiscovery/httpx
- Paramspider:https://github.com/devanshbatham/ParamSpider
- Kxss ou GF:https://github.com/Emoe/kxss//https://github.com/tomnomnom/gf
for URL in $(</root/recon/target/httpx); do (python3 paramspider.py -d "${URL}");
done;
- coletando todos os domínios que estão no escopo
- executando o Subfinder usando o seguinte comando
subfinder -dL domains.txt -o subfider-subdomains.txt
cat domain_list.txt | assetfinder --subs-only > assetfinder-subdomains.txt
cat subfinder-subdomains.txt assetfinder-subdomains.txt > subdomains.txt
sort -u subdomains.txt > sort.txt
cat sort.txt | httpx -mc 200 > 200_urls.txt
for URL in $(</root/recon/target/200_urls.txt); do (python3 paramspider.py -d "${URL}");
done
cat filtered_urls.txt | kxss


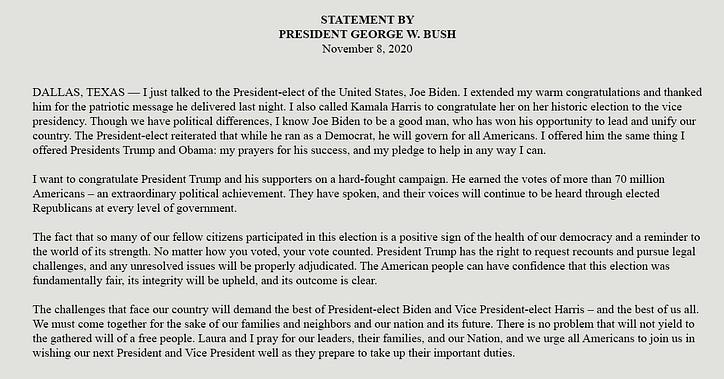
George Harrison ficou chateado por suas letras de 'Hurdy Gurdy Man' de Donovan não terem sido usadas








































![O que é uma lista vinculada, afinal? [Parte 1]](https://post.nghiatu.com/assets/images/m/max/724/1*Xokk6XOjWyIGCBujkJsCzQ.jpeg)